Security engineering leader, DFIR practitioner, and published author
Projects

Luminaut
Luminaut is a utility to scope cloud environment exposure for triage. The goal is to quickly identify exposed resources and collect information to start an investigation.
Starting from public IP addresses of AWS and GCP resources, Luminaut gathers information about associated instances, load balancers, security groups, and related events. The framework also includes active scanning tools like nmap and whatweb, to identify services running on exposed ports, and passive sources like Shodan.
By combining cloud configuration data with external sources, Luminaut provides context to guide the next steps of an investigation.
Presented at
ShmooCon 2025
BSides Las Vegas 2025
Black Hat Arsenal 2025
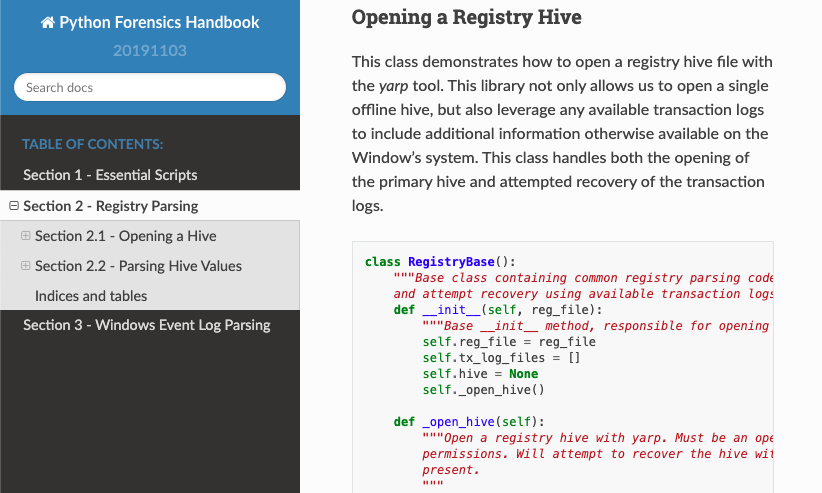
Python Forensics Handbook
Free reference for common tasks encountered when implementing DFIR scripts. These short snippets provide copy/paste templates to use to start parsing registry hives, analyzing Windows events, and reporting on JSON data. Open for contributions on GitHub and for use in your project!
Website GitHub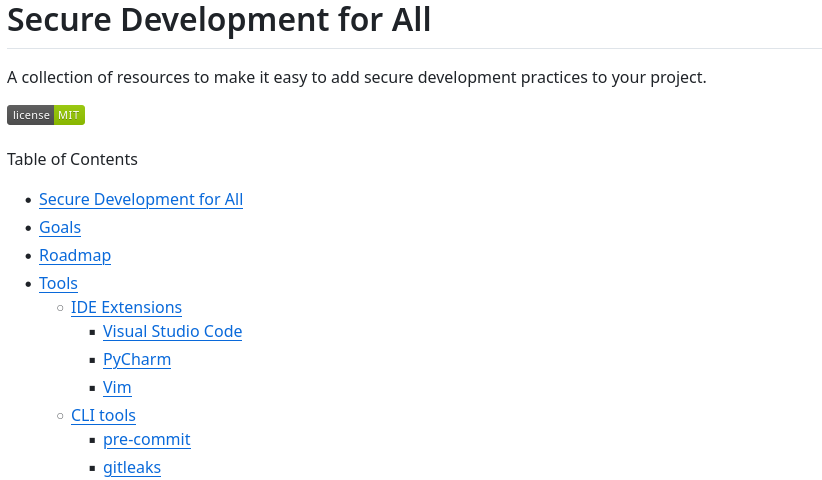
Secure development for all
A collection of resources to ease the process of integrating secure development practices. Includes a roadmap with suggested tools and how to install and configure them.
GitHub
RDP Snitch Honeypot
A honeypot that you can set up in a weekend to capture RDP traffic and share out findings via a Mastodon/Twitter/Pastebin bot. Includes enrichment of the observation and aggregation of statistics.
Blog Series MastodonBooks
Python Digital Forensics Cookbook
2018 DFIR Book of the Year, Forensic 4:Cast Awards
This book exhibits many of the Python libraries commonly used in digital forensics through small scripts (or recipes). Across the 60+ recipes, we explore how to process files with embedded metadata, parsing common file and registry artifacts, processing evidence stored as E01 files, integrating Python with common tools such as Axiom, EnCase, and Cellebrite, and much more. This book is available as Paperback & E-Book.
Packt Publishing Amazon GitHub
Learning Python for Forensics
Learn the art of designing, developing, and deploying innovative forensic solutions through Python scripting. Starting with the basics and building on them chapter by chapter with practical examples. This book is available as Paperback & E-Book.
Packt Publishing Amazon GitHub